Vulnerability Scanning
The Vulnerability Scanning application is a comprehensive vulnerability assessment system that is built to detect, and flag known and potential security weaknesses in servers and user devices located in the Crystal Eye network or elsewhere.
The application has enhanced capabilities to perform vulnerability scan of:
- Servers and user devices in the Crystal Eye network,
- Servers or user devices located outside the Crystal Eye network, or
- Specific website page
Note: Ensure that ICMP is enabled on the devices in the CE network before the vulnerability scan is initiated if you do not intend to use the “Assume Alive” option.
The application is programmed to scan all default port types. However, the Crystal Eye administrator can also specify the custom ports to be scanned. The fully automated system of the Vulnerability scanning application enables CE administrators to identify security loopholes in the network and classify weaknesses that might lead to a security incident. It helps in predicting the effectiveness of the various countermeasures taken to secure networks and assists in remediating any risks that are targeted towards external facing servers deployed in the Crystal Eye network.
Note: Vulnerability Scanning is a paid service. However, the eCISO service includes a quarterly vulnerability scan as a part of the service.
There are three types of scanning available:
- Deep – Non Destructive Full and Slow Scan,
- Default – Non Destructive Full and Fast Scan, and
- Ultimate – Full and Fast Scanning Including Destructive.
Scheduling is handled via the Task Scheduler which allows for flexible management of Vulnerability Scanning and other functions.
Note: Once the vulnerability scan is completed it can take up to 3 business days for the report to be available in the Orchestrate client dashboard depending on the size of the network being scanned and selected options.
Warning: Running a vulnerability scan during business hours poses a risk to availability of business services. There is a possibility of interruptions to business-critical services like phones and internet. The recommendation is to leave devices to be scanned powered on and then running scans overnight. A scan during business hours may capture more active devices, but the increased risks of service interruption should be given serious consideration by the business prior to scheduling a Vulnerability Scan.
Vulnerability Scanning and Operation Technology: Due to the increased risk of unpredictable behaviour of OT systems while being scanned for vulnerabilities, special consideration of OT segregation and Vulnerability Scan timing is recommended. Best practices recommend that OT systems are monitored for availability during scans and that OT networks are scanned separately to IT systems. It is also highly recommended that OT systems are not exposed to external threats via the Internet.
The Vulnerability Scanning application is not available by default. It can be installed from Marketplace in the left-hand navigation panel.
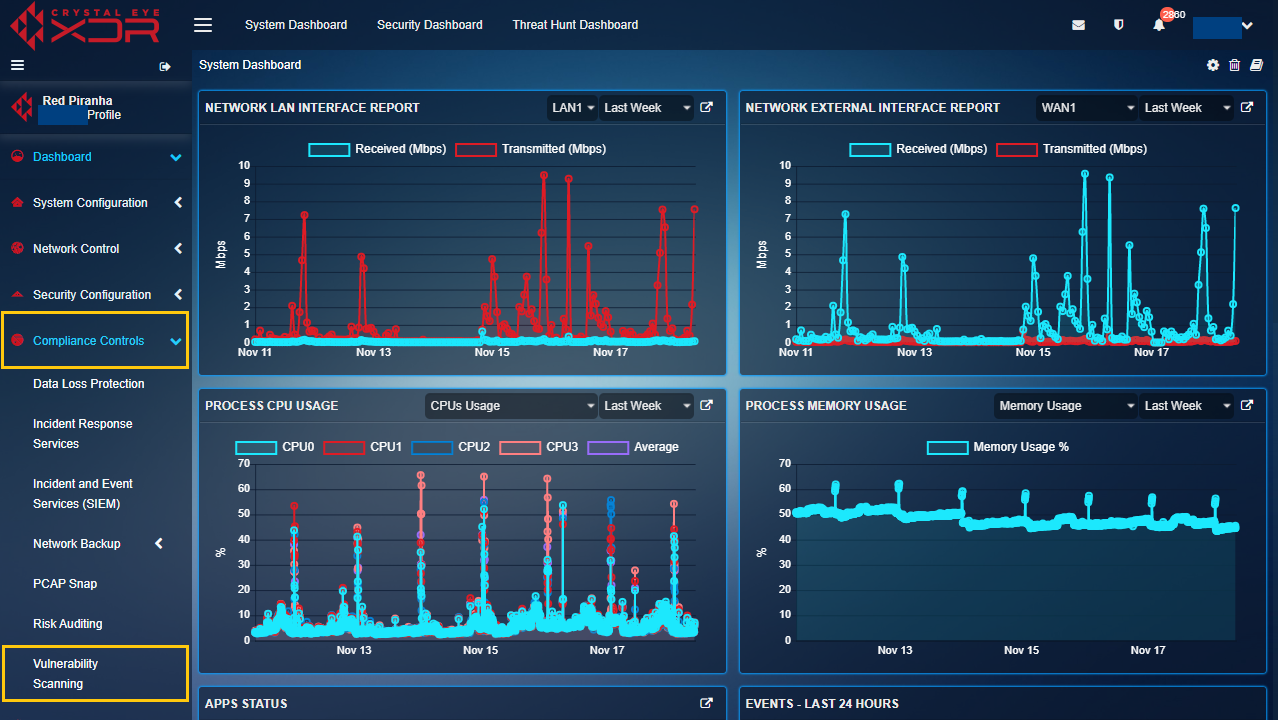
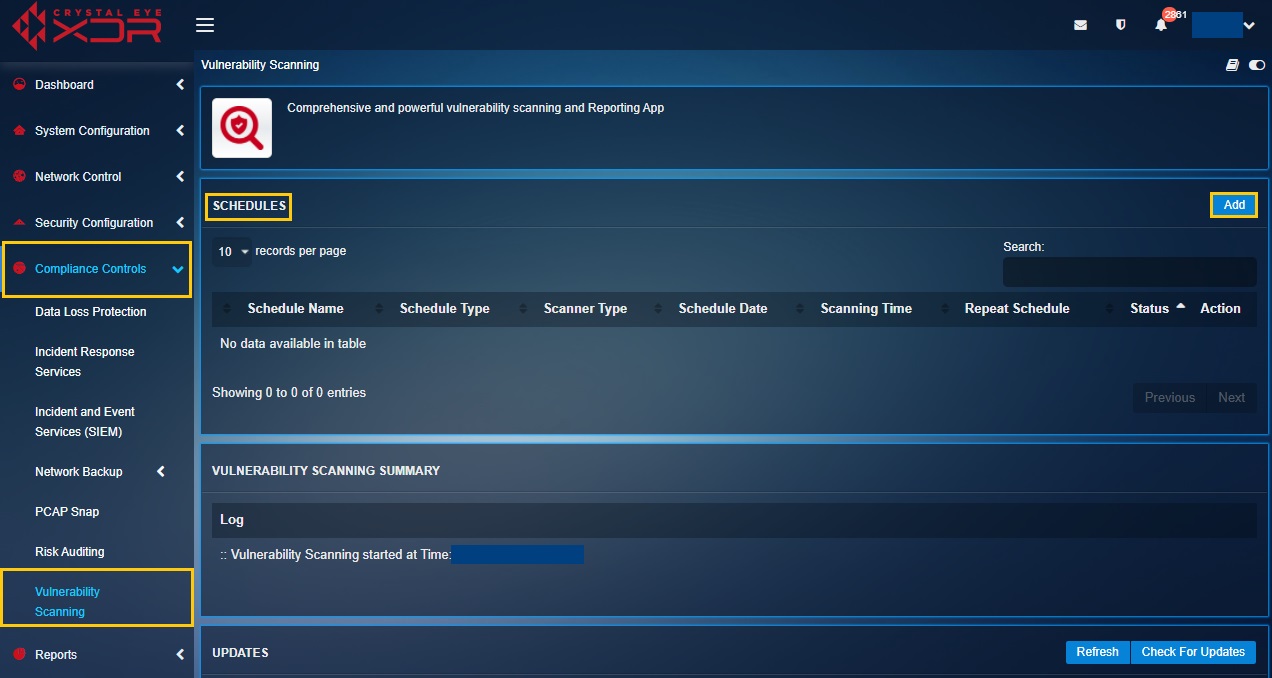
Left-hand Navigation Panel > Compliance Controls > Vulnerability Scanning
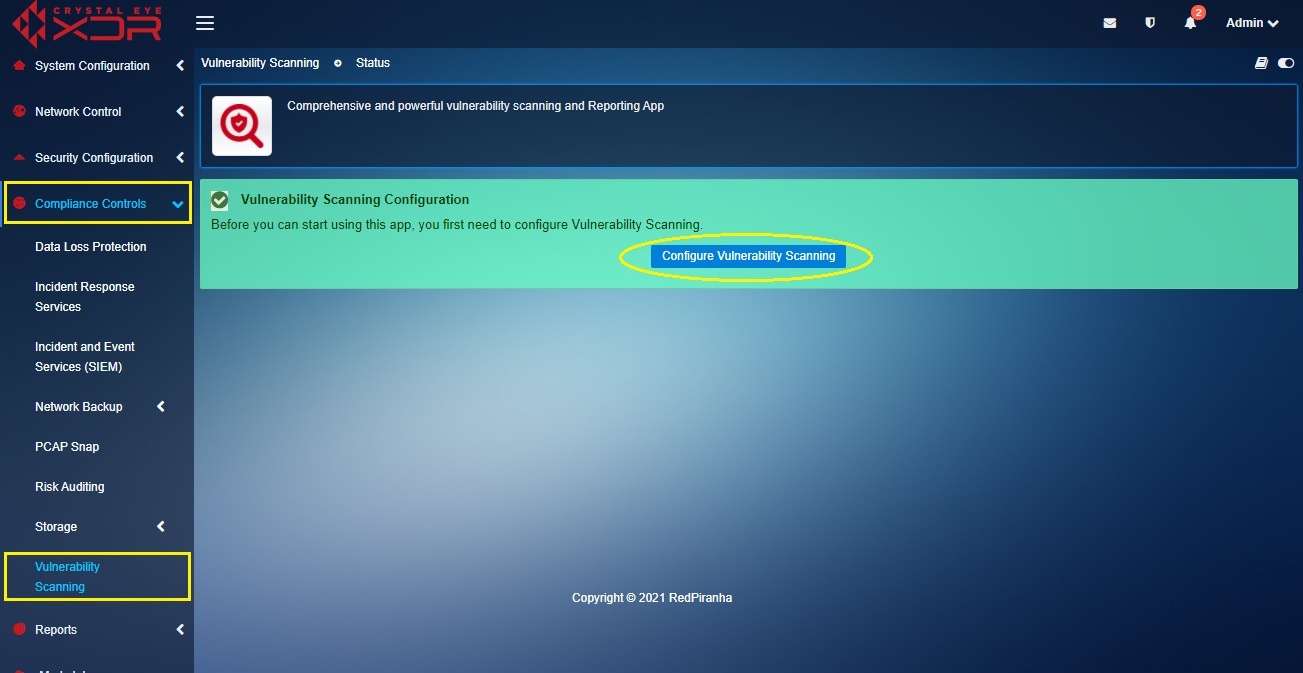
The Vulnerability Scanning application needs to be configured before it can be used.
WARNING : During configuration of Vulnerability Scanning application or execution of Vulnerability Scans multiple database transactions may be in progress. Interrupting these transactions may result in database corruption that will require Level 3 engineers to resolve. Power cycling/restarting or shutting down of the appliance during either of these activities are not supported and will attract a fee if logs show that power interruption was performed at the time of failure. Advice is to not interrupt power or otherwise take actions that would interrupt the configuration of the Vulnerability Scanning application or execution of Vulnerability Scans.
How to Configure Vulnerability Scanning Application?
Step 1: In the Vulnerability Scanning application page, click the Configure Vulnerability Scanning button.
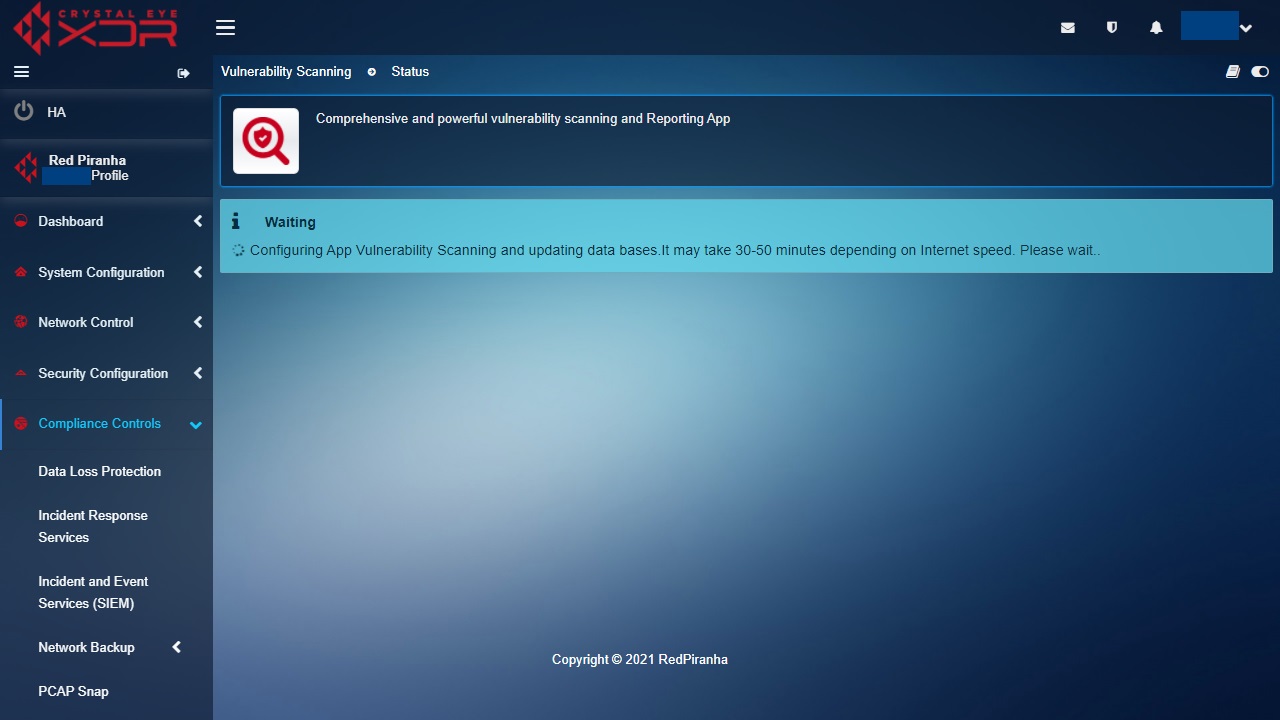
The configuration process will then commence while displaying the screen below:
To schedule a Vulnerability Scan a Crystal Eye administrator must select the Schedule Type.
There are three Schedule Types supported by Crystal Eye namely:
- Crystal Eye (Entire Network),
- Scan Custom Location, and
- Scan Web Page.
If the Crystal Eye (Entire Network) type is selected, then the vulnerability scanning application would scan all the servers and user devices connected to the Crystal Eye appliance.
Scan Custom Location is selected when there is a requirement to scan external servers and user devices. The CE administrator would have to provide the IP address of the external server or user devices while scheduling the scan.
Use the Scan Web Page schedule option if a particular website needs to be scanned for known and potential vulnerabilities.
Note: The Vulnerability application GUI also provides the option to exclude Hosts from the scheduled vulnerability scan. Please be advised that this option to exclude hosts only exists when a Crystal Eye (Entire Network) schedule type has been initiated.
Another important aspect about this application is that the CE administrator can define whether to scan default ports or custom ports. The CE administrator can opt for various scanner types while scheduling vulnerability scans such as Deep – Non Destructive Full and Slow Scan, Default – Non Destructive Full and Fast Scan and Ultimate – Full and Fast Scanning Including Destructive.
Based on the policy requirements of the organisation, the Crystal Eye administrator can also specify whether vulnerability scans are to be scheduled on a one time basis, weekly basis or a monthly basis. Based on how the CE administrator chooses to repeat the schedule of the vulnerability scan a specific date and time can be scheduled.
How to Add a New Vulnerability Scan Schedule?
Step 1: In the Vulnerability Scanning application page, click the Add button in the Schedules section.
Step 2: You will now see the Add New Vulnerability Schedule page. Enter the Schedule Name in the textbox.
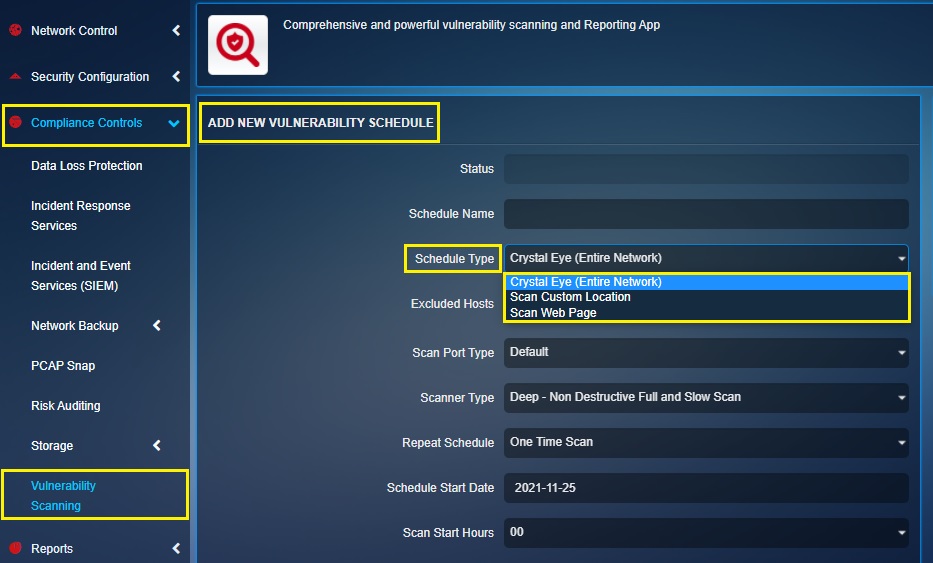
Note: The Schedule Type feature of Crystal Eye’s Vulnerability Scanning application is such that the CE administrator can opt to run a vulnerability scan on the Entire Crystal Eye network, a custom location in the external zone of the CE or a particular web page.
Step 3: Select the Scan Port Type from the dropdown so as to specify whether to scan a default port or a custom port.
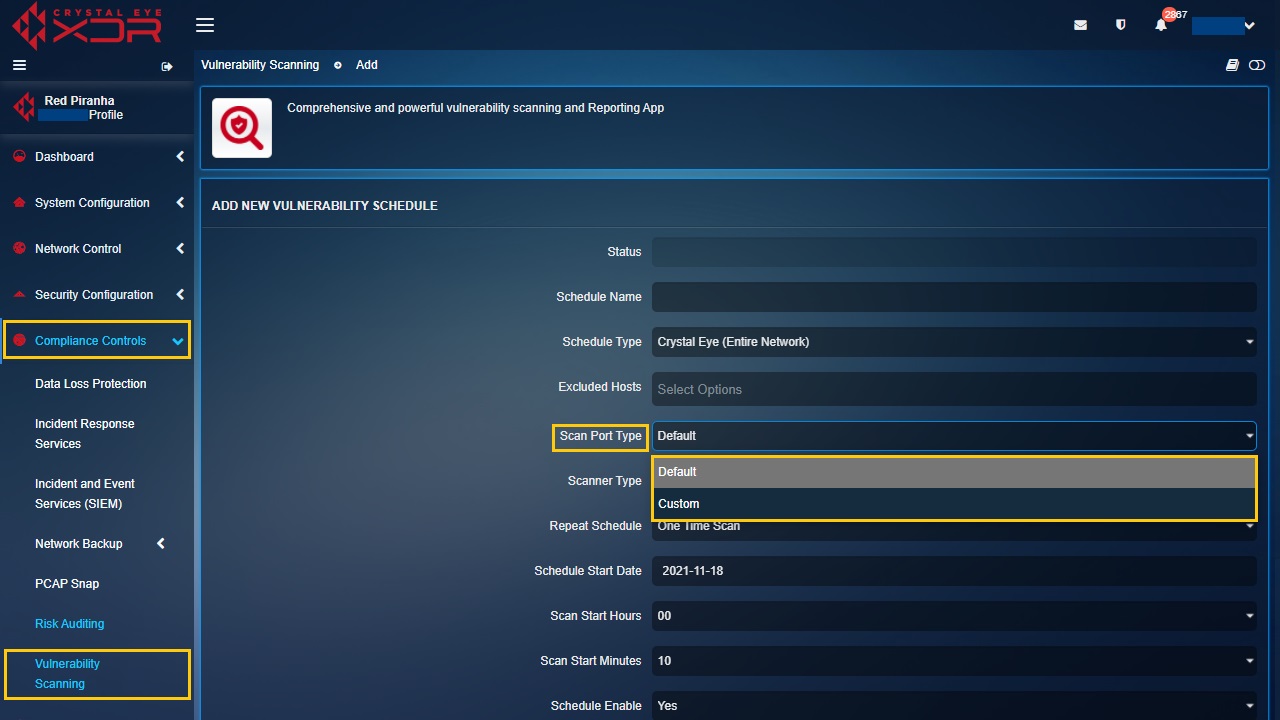
Note: If you select Custom from the dropdown, the Custom Ports textbox will appear below. Please be advised that the writing format to be followed while entering the TCP port range and port details is T:3-5 and T:6 whereas, the writing format to be adhered while entering UDP port range and ports in the text box is U:7-9 and U:10.
Step 4: Select the Scanner Type from the dropdown.
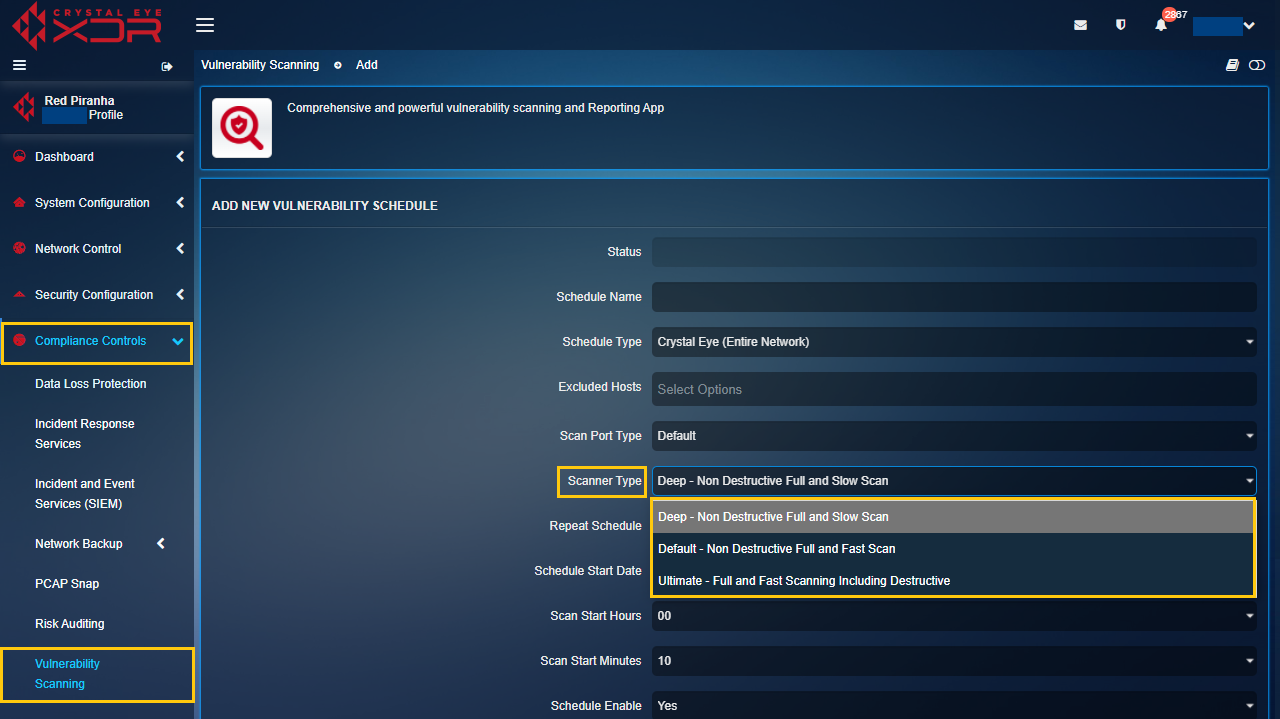
Note: The scanner type is the depth to which the vulnerability scan would be done. The 3 scanner types that can be selected are Deep – Non Destructive Full and Slow Scan, Default – Non Destructive Full and Fast Scan, and Ultimate – Full and Fast Scanning Including Destructive.
Step 5: Select from the dropdown and specify whether it’s a One Time Scan, Weekly Scan or a Monthly Scan.
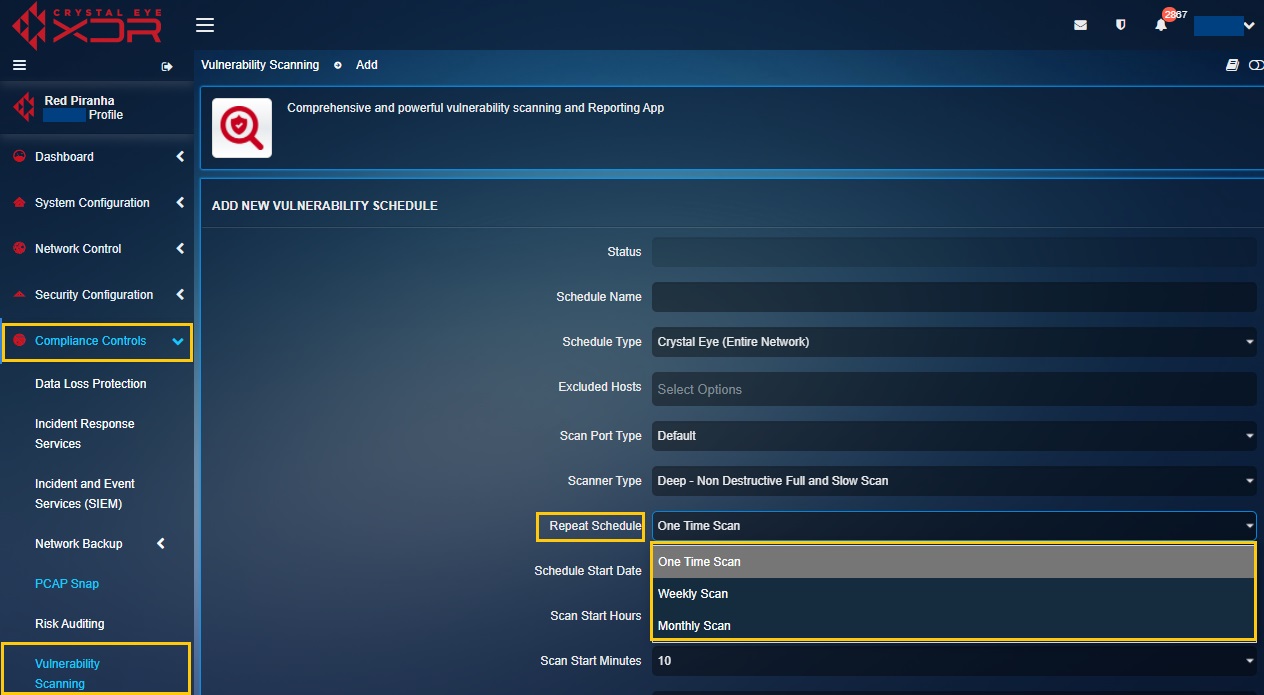
Note: If One Time Scan option is selected then a start date and time must be specified. Likewise, if Weekly Scan is selected then the CE administrator must specify the start date, end date, days of the week, and time. However, if the CE administrator’s wishes to select Monthly Scan option then the start date, end date, month date, time must be selected.
Step 6: After specifying the date, time, and day, click the Add button.
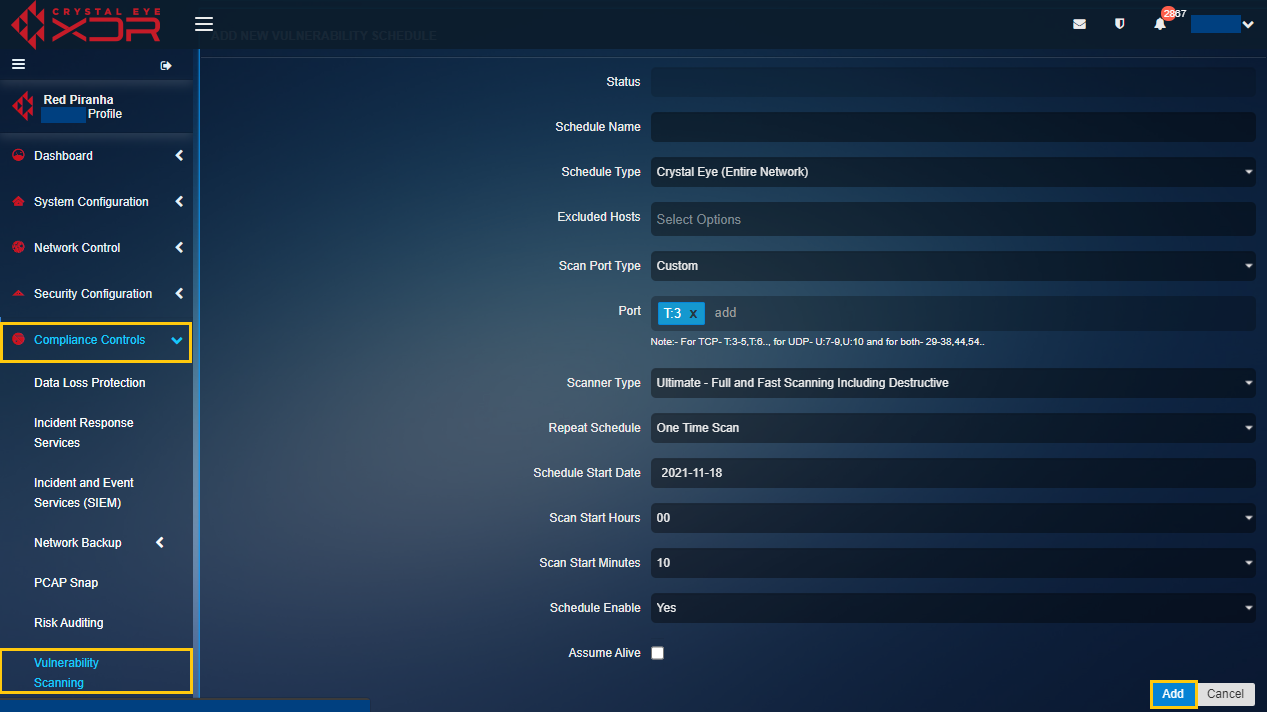
Note: To ensure scanning of devices which are not responding to ping requests, select the Assume Alive tick box as shown below. This will provide a more comprehensive scan result but may result in a longer scan time. 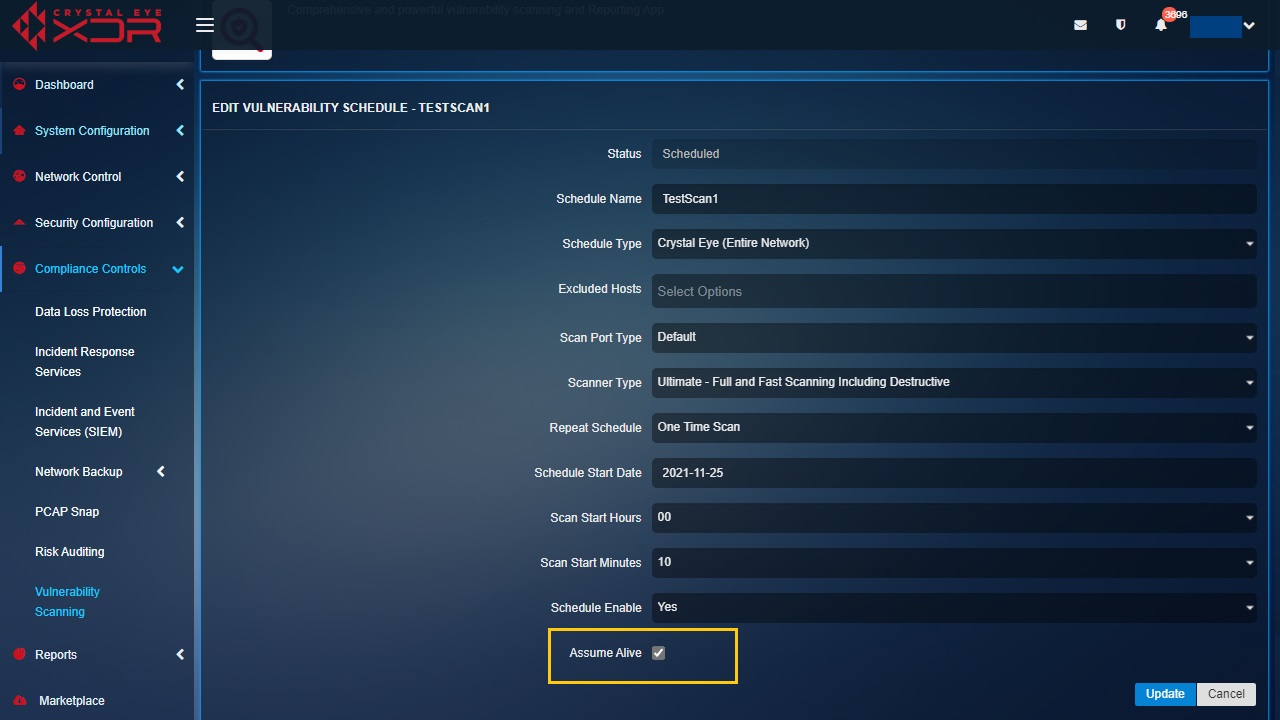
Step 7: You will now be directed to the Vulnerability Scanning application page. The vulnerability scan details would appear in the Schedules section.
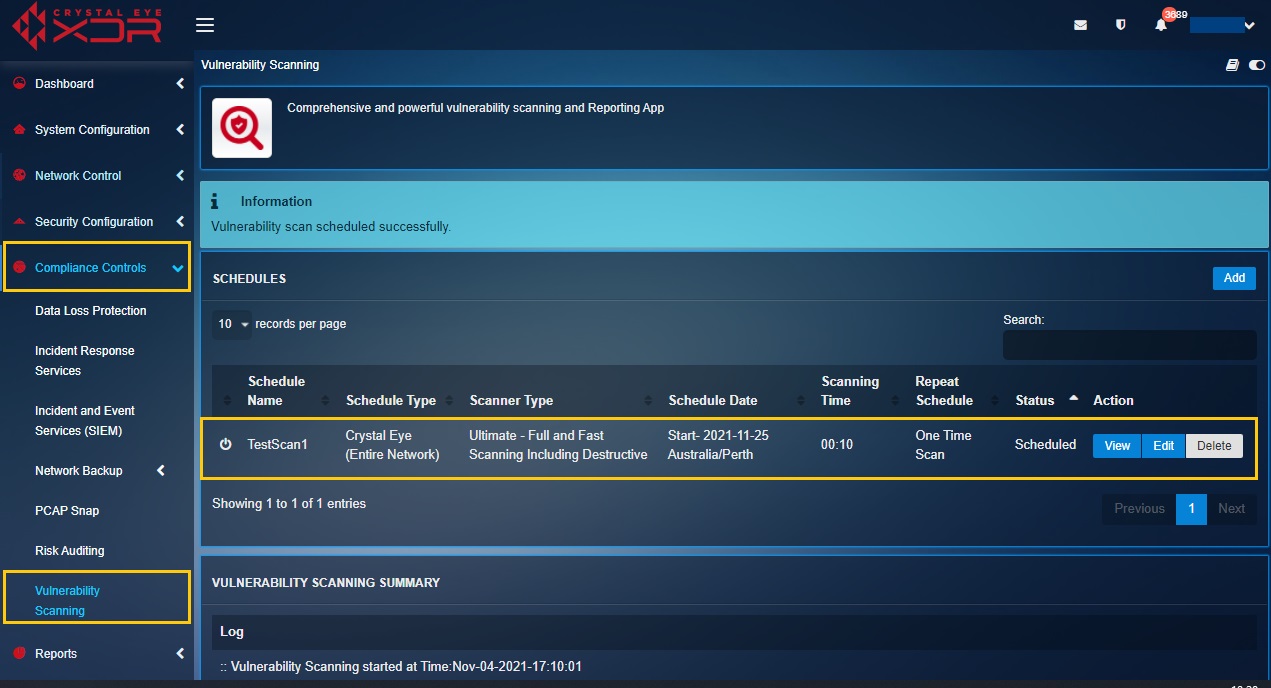
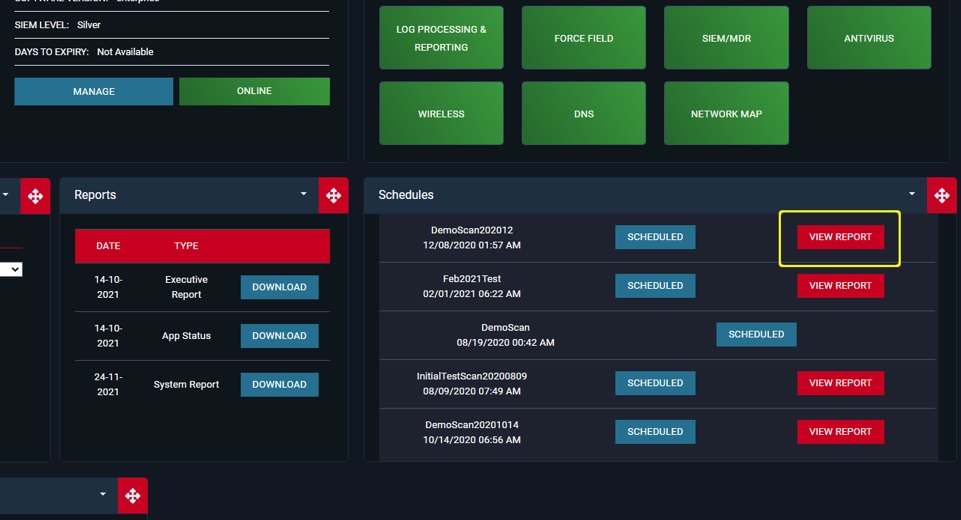
Note: Once the Vulnerability Scan has been scheduled the Status section will show whether the scan is ‘Scheduled’, ‘Running’, or ‘Completed’. Refer to the screenshot below.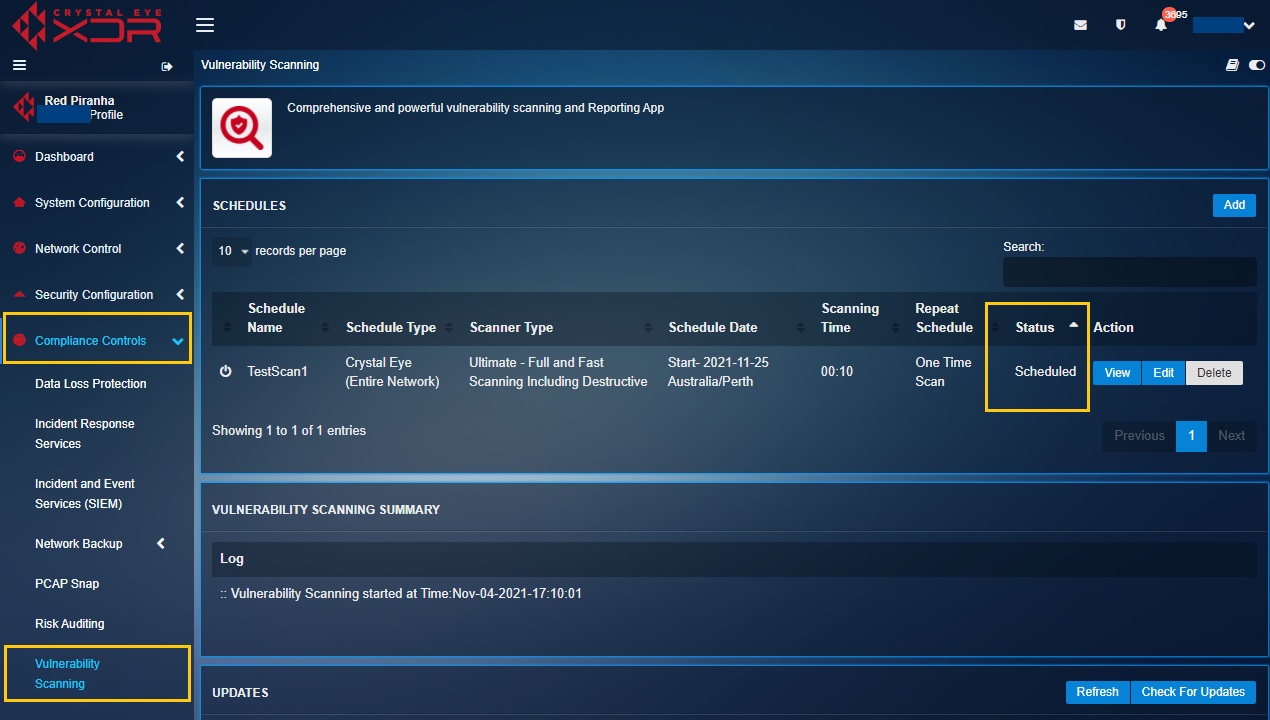
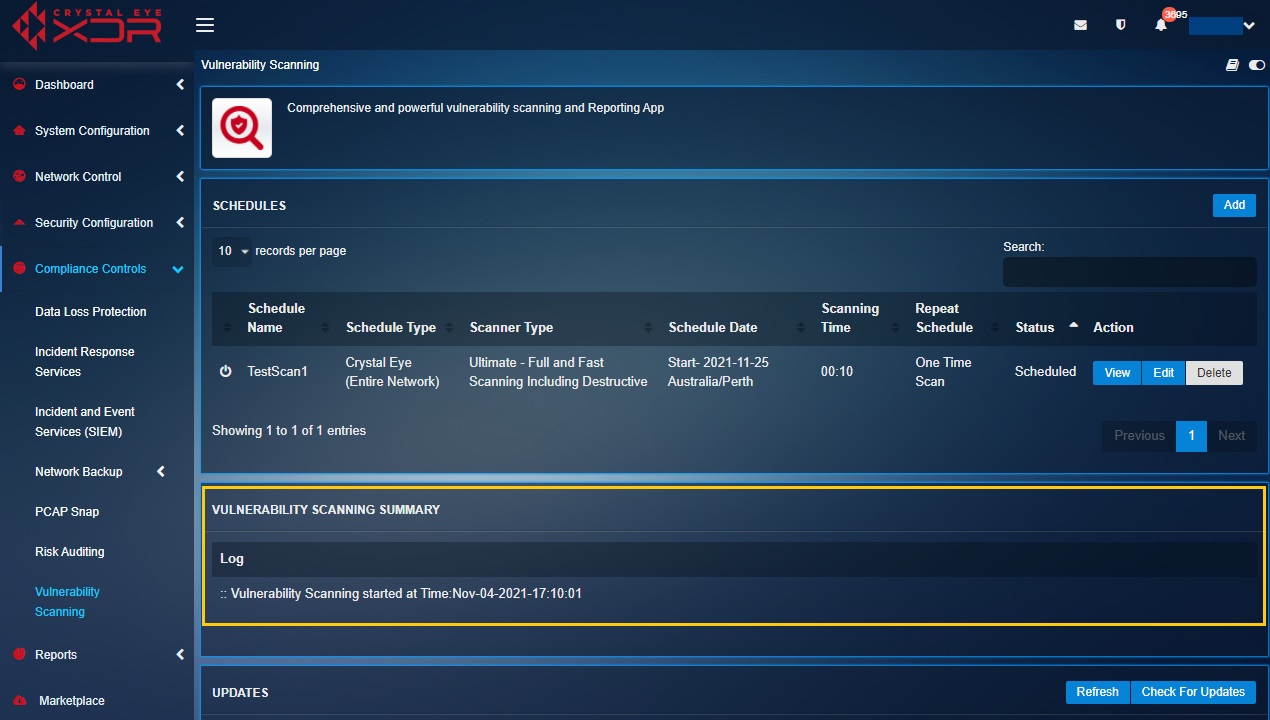
The Vulnerability Scanning Logs provides a comprehensive view of the date and time at which a scan was initiated or stopped. Apart from this the scan schedule details are also displayed upon scan completion.
The screenshot below shows an example of the vulnerability scanning log details:
The Vulnerability Scan Report appears in Red Piranha’s client dashboard after the scan is completed. However, it must be noted that it takes 3 business days for the report to be generated and made available for download.
The report can be downloaded in PDF format from Red Piranha’s client dashboard. The dashboard can be accessed using the same user credential that was used while registering the Crystal Eye appliance.
Note: The report can either be viewed on the client dashboard or it can be downloaded in PDF format.
How to View the Vulnerability Scan Reports in the Client Dashboard?
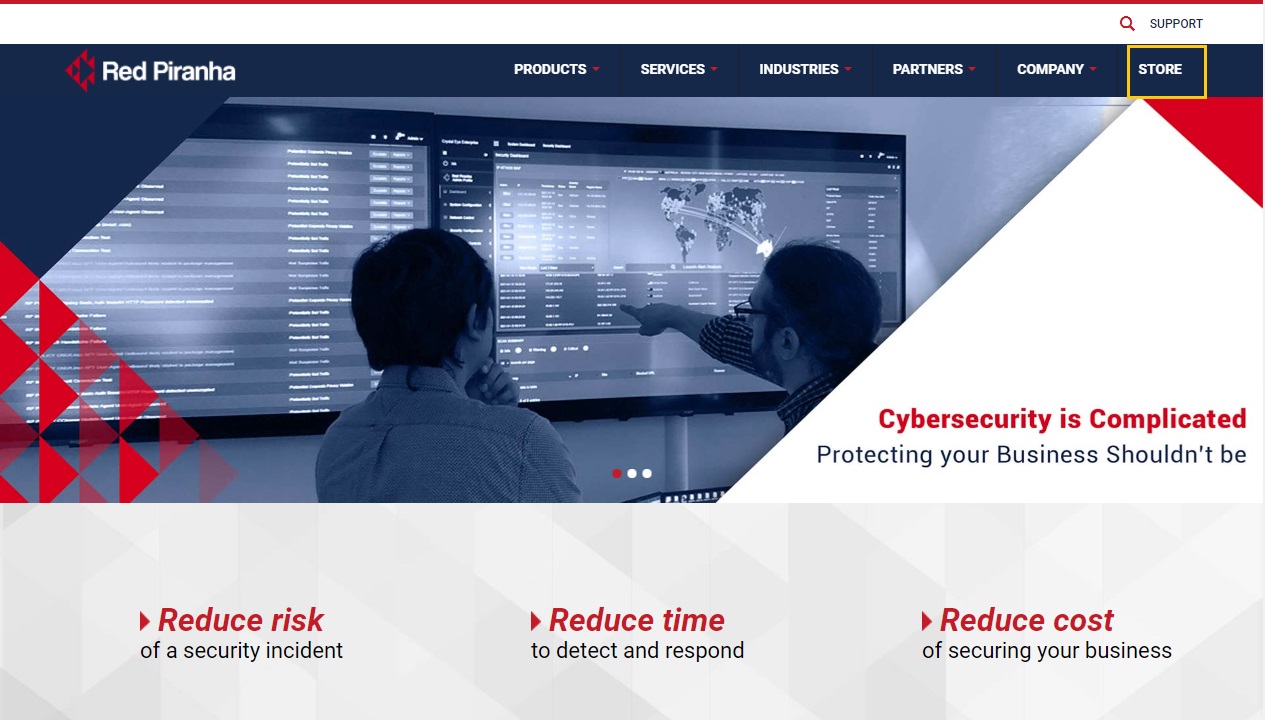
Step 1: Go to https://www.redpiranha.net/
Step 2: Click the Store button on the homepage navigation panel.
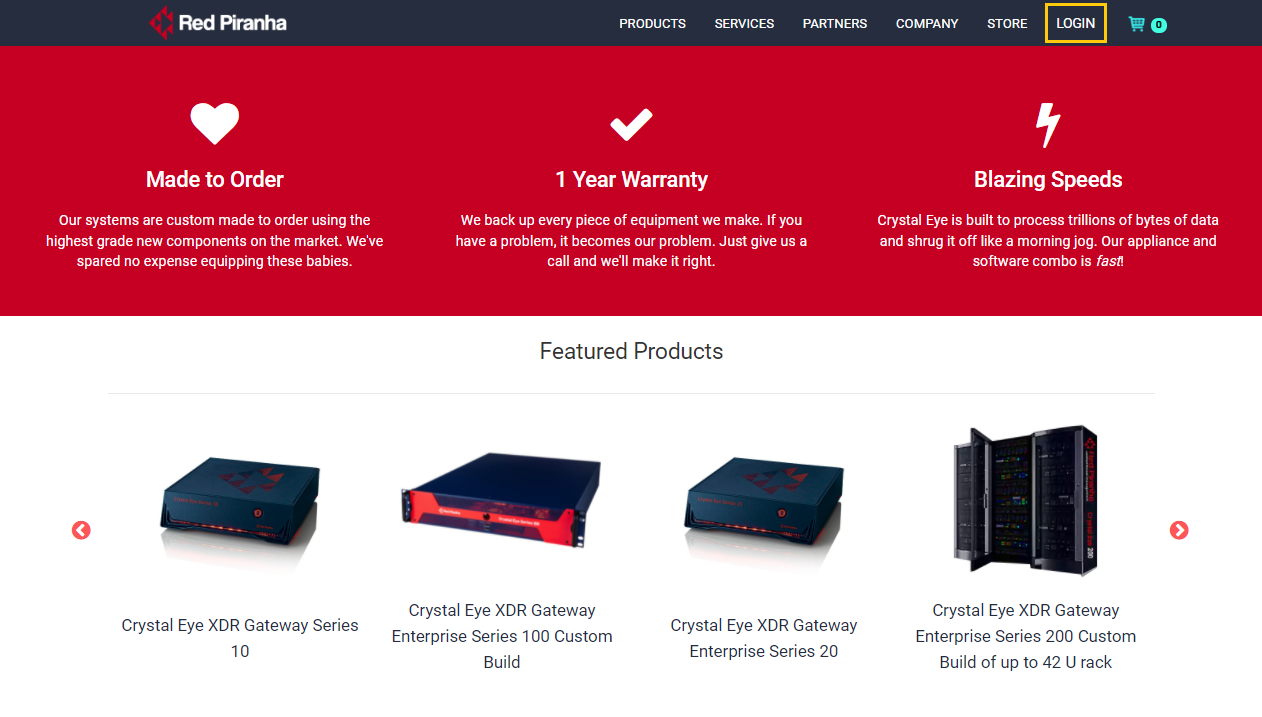
Step 3: You will now be directed to Red Piranha’s Store Website. Click the Login button on the top-right corner of the web page.
Step 4: You will now see a Login pop-up box. Enter your user credentials and click the Login button.
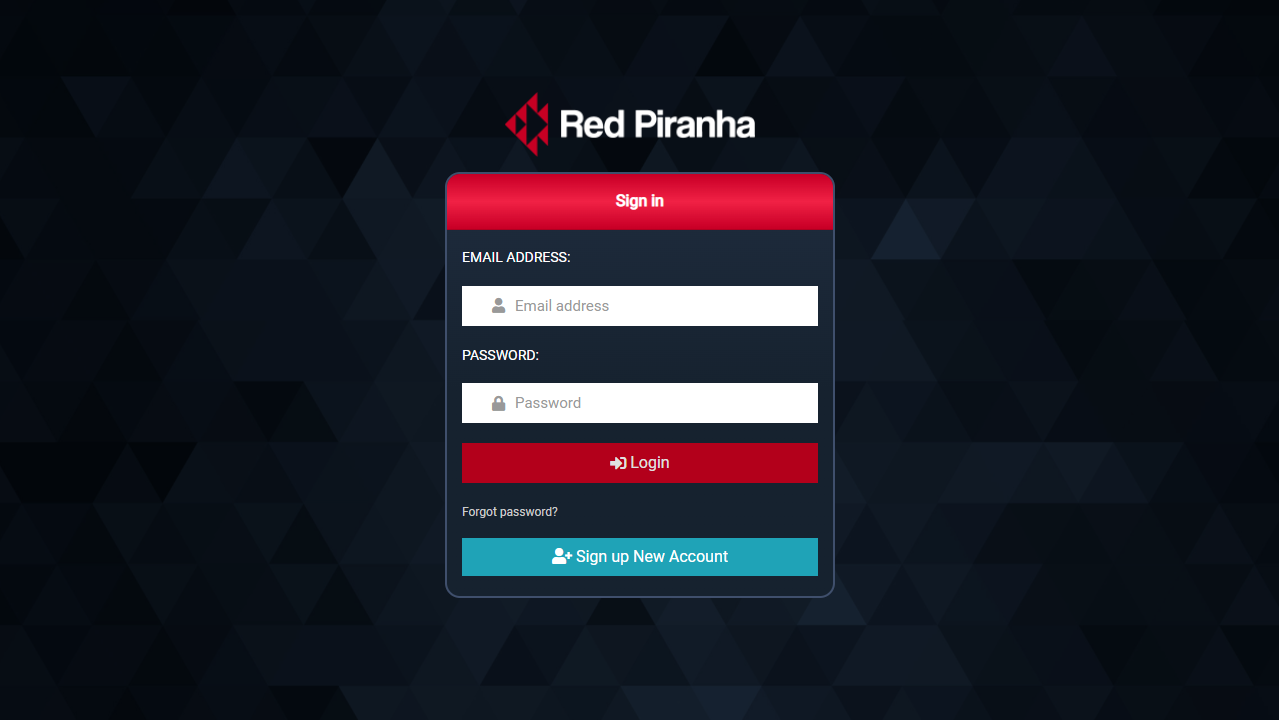
Note: Enter the email account and password that was used while registering the Crystal Eye appliance. You may re-generate the password through the forgot password feature in case you lost/forgot it.
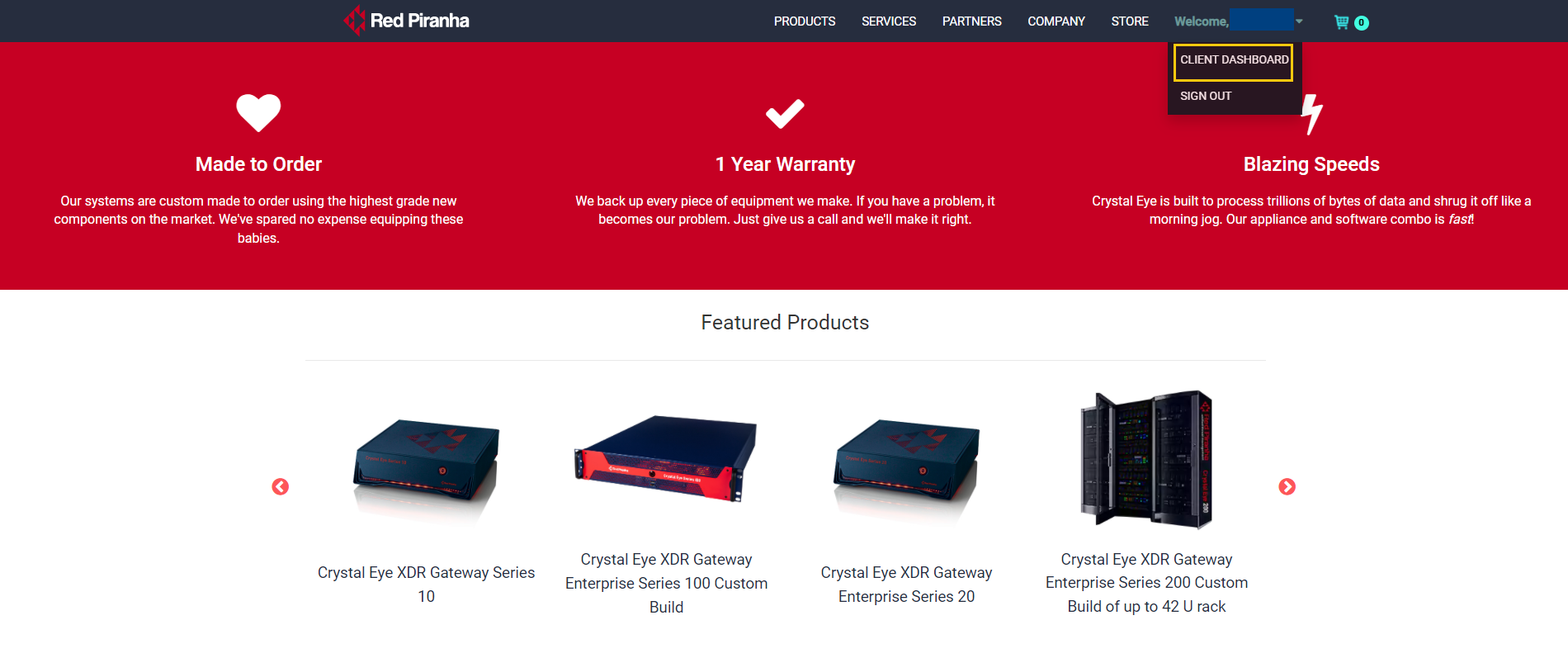
Step 5: Select Client Dashboard from the Welcome dropdown.
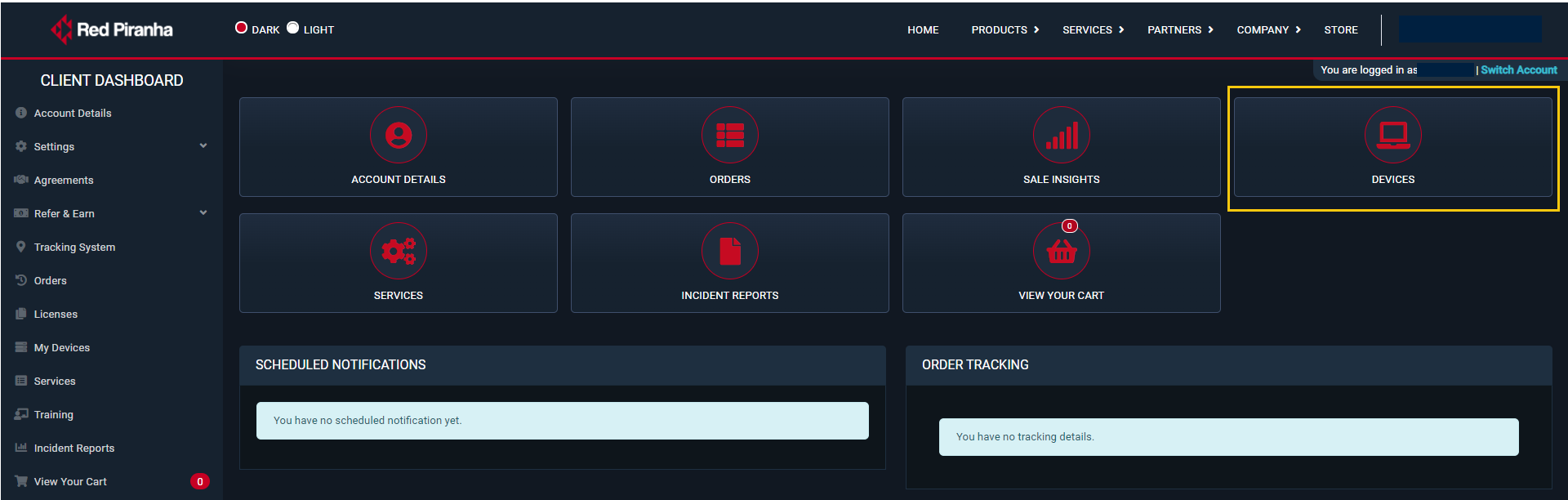
Step 6: You will now be directed to the Client Dashboard. Click the Devices button.
Step 7: You will now see the list of devices. Click the View button next to the device name where the vulnerability scan was scheduled.
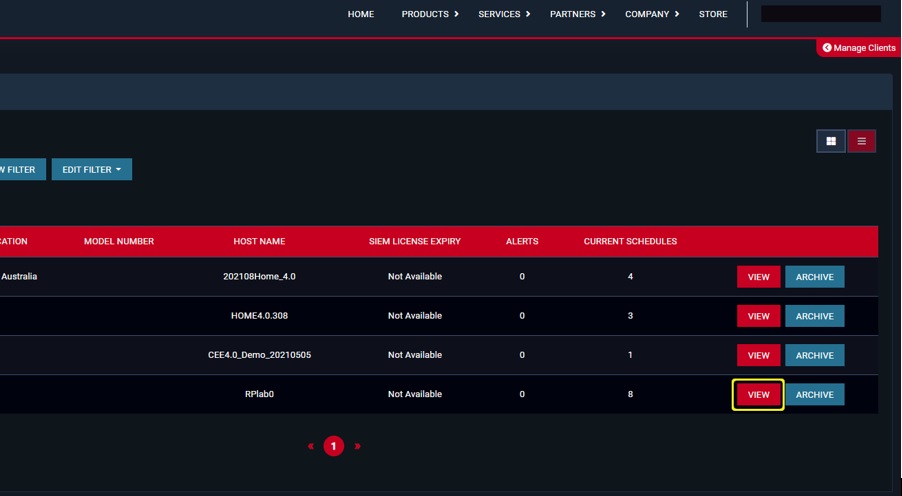
Step 8: You will now see the Vulnerability Scan Report in the schedules section of the dashboard. Click the View Report button to explore the report and access the Export to PDF function.
Crystal Eye XDR’s vulnerability scan report consists of the following components.
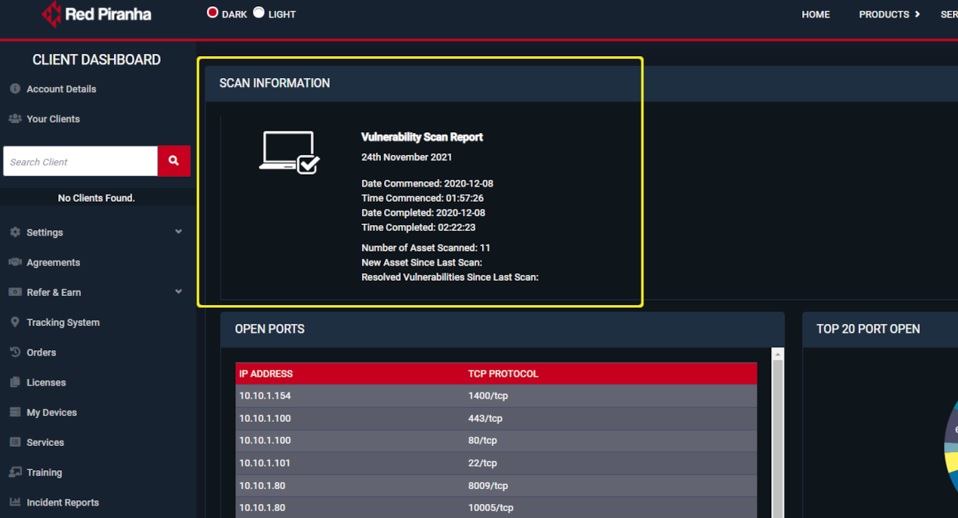
Scan Information: Displays the date on which the report was downloaded, the commencement and completion date & time of the scan, number of assets scanned, new asset since last scan (if any), and resolved vulnerabilities since last scan (if any). Refer to the screenshot below.
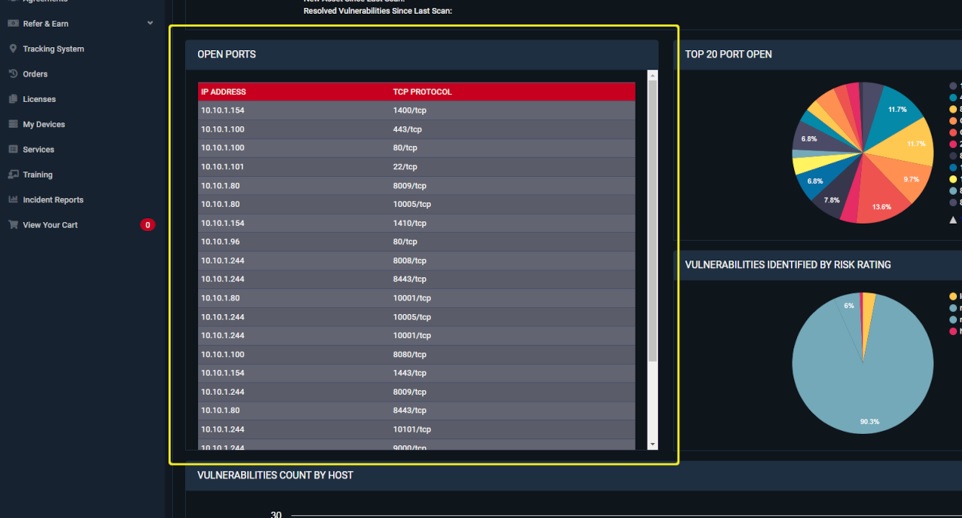
Open Ports: This section displays open TCP ports in hosts connected to the CE XDR in a tabular format (Refer to the screenshot below).
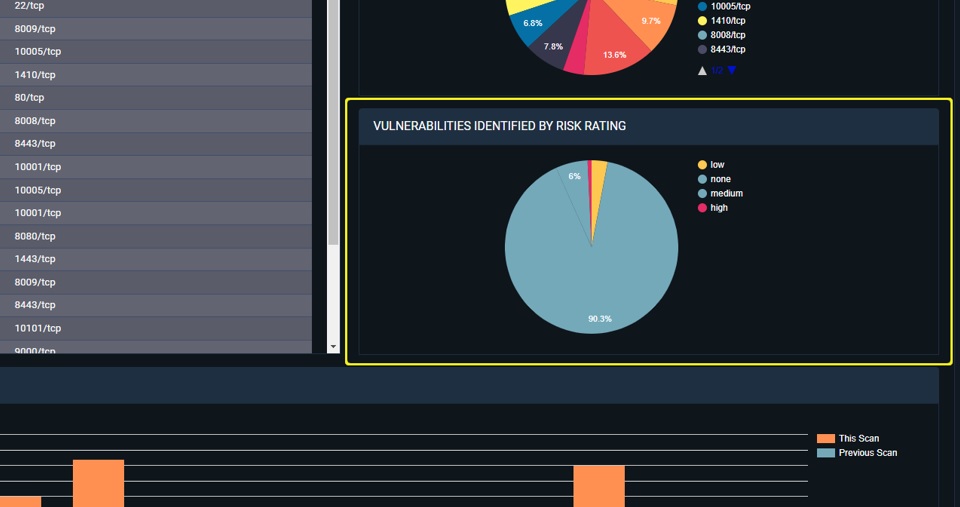
Top 20 Open Ports: This pie chart provides insights on the top 20 ports open in the hosts scanned by the CE XDR (Refer to the screenshot below).
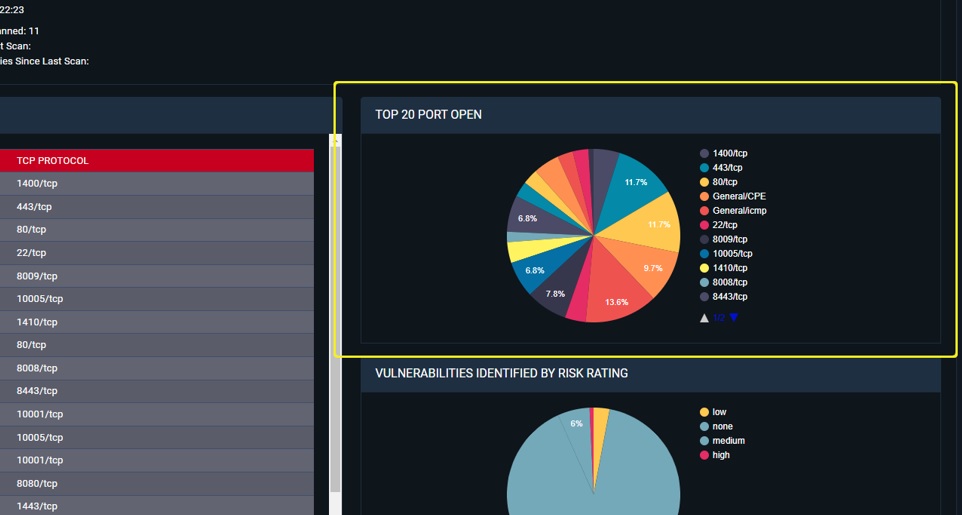
Vulnerabilities Identified by Risk Rating: This pie chart quantifies the vulnerabilities identified during the scan as per its risk rating which could be low, medium, or high (Refer to the screenshot below).
Vulnerabilities Count by Host: This bar graph shows the total number of vulnerabilities found in each host scanned by the CE XDR (Refer to the screenshot below).

Host Count by CVE: This bar graph provides insights on the total number of hosts aligned with a particular vulnerability CVE (Refer to the screenshot below).

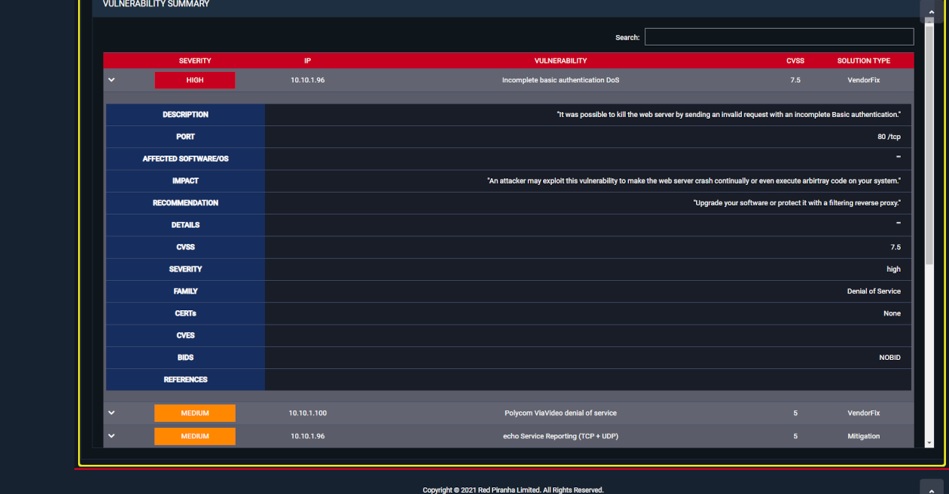
Vulnerability Summary: The summary is displayed in a tabular format containing information about the severity levels of the vulnerability found in the hosts scanned by the CE XDR. Clicking on a particular entry provides insights on the CVSS score of the vulnerabilities and suggests a solution type which could either be that a vendor patch is available (Vendor Fix), a mitigation by configuration is available (Mitigation), a workaround is available, and no solution exists (Refer to the screenshot below).